Any kind of policies you rely on should be based on a sound understanding of risks, vulnerabilities, and defenses. “Best practice” is intended as a default policy for those who lack the data, resources, funding or training to do their own risk assessments to define their own standards. Regular password change is a long-standing security practice. It was designed to periodically lock out unauthorized users who had learned users’ passwords. Some security experts began questioning the wisdom in enforcing regular password change over a decade ago. However, it is only in the last few years that published research provided evidence that this practice may indeed be less beneficial than previously thought. And even retrogressive.
So how often should you change your passwords?
So today’s million-dollar question is, how often should you change your passwords?
Conventional wisdom held that you should change your passwords regularly, typically every few months; for instance, at least every three months. For years, this was the recommendation given by many cyber security experts. The rationale was that if a password is compromised, the time that an attacker has unauthorized access to the compromised account will not be indefinite.
While this notion sounds sensible, over time, security experts have changed their views on the matter. In 2017, the National Institute of Standards and Technology (NIST) released Digital Identity Guidelines that changed the password security game.
Unless you are aware or suspect that your password has been compromised or shared, changing your password frequently may do more harm than good.
There is really no need to change your password regularly. You just need to put in the time and effort to ensure the password you create is strong and unique. In addition, using multi-factor authentication is highly advisable as an additional measure to secure your account.
When users are forced to make password changes, few will make stronger passwords. They will tend to change them in predictable ways that are more easily compromised by attackers. For example, a password that had “P@$$w0rd” becomes P@$$w0rd1, and so on.
Important note: Even where a password has been compromised, changing the password alone may be ineffective. It is essential to take other steps to secure the account to prevent recurrent compromise.
Even Microsoft Agrees
Microsoft termed periodic password expiration settings as an “ancient and obsolete mitigation of very low value.”
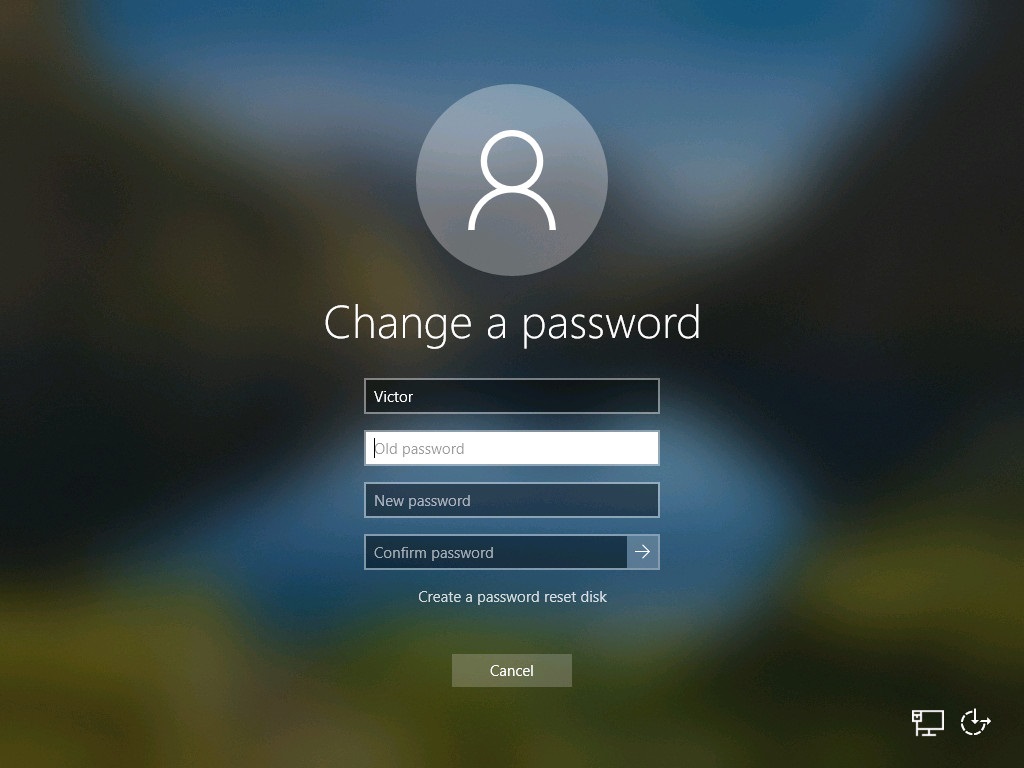
“There’s no question that the state of password security is problematic and has been for a long time. When humans pick their own passwords, too often they are easy to guess or predict. When humans are assigned or forced to create passwords that are hard to remember, too often they’ll write them down where others can see them.”
Source: Microsoft Security Baseline for Windows 10 v1903 and Windows Server v1903
It proceeds to say:
When humans are forced to change their passwords, too often they’ll make a small and predictable alteration to their existing passwords, and/or forget their new passwords. When passwords or their corresponding hashes are stolen, it can be difficult at best to detect or restrict their unauthorized use.”
Source: Microsoft Security Baseline for Windows 10 v1903 and Windows Server v1903
What to do instead of Changing Your Password Frequently
Instead of forcing frequent password changes, we recommend the following:
- Create a strong, long and unique password.
- Do not write down or share your password with anyone.
- Do not save your passwords on any browsers, especially when accessing your email or accounts on public computers.
- Wherever possible, use multi-factor authentication. Multi-factor authentication adds extra protection so that even if your password is compromised, the attacker will not automatically access your account.
- If you suspect that your account has been hacked, change your password immediately – do not wait for a prescribed number of days. Mandatory password changes provide little security benefit after a password breach has already occurred.
“Periodic password expiration is a defense only against the probability that a password (or hash) will be stolen during its validity interval and will be used by an unauthorized entity. If a password is never stolen, there’s no need to expire it. And if you have evidence that a password has been stolen, you would presumably act immediately rather than wait for expiration to fix the problem.”
Source: Microsoft Baseline
If you are an administrator, consider championing the development and adoption of security strategies for your company like:
- Set policies to lock accounts after multiple failed login attempts to minimize chances of successful brute force attacks and password cracking. Brute force and password cracking methods have to run multiple password combinations in an attempt to gain unauthorized access.
- Use technology to disallow setting passwords that are commonly used and known/already-compromised.
- Implementing additional layers of security to enhance system and user account security, including gateway and end-point security and a good email security solution. Get in touch with us for more information on our advanced email security service or…
NB: This list is a baseline and should not be considered an exhaustive checklist. Adopt your own security strategy based on a risk assessment of your environment.
Summary
Research shows that the time-honored practice of forcing regular password change has fallen out of favor over time.
If you have a strong and unique password, you don’t need to change it unless you believe it has been compromised.
![]()